Editor’s Note: This is the first of two parts examining AI-powered cybercrime targeting wholesale distributors. Part One documents the scale of the threat, including four major distributor breaches producing more than $1 billion in combined damage, drawing on field research and interviews with fraud expert J. Michael Skiba and technology consultant Tim Bertschmann. Part Two, publishing next week, examines what distributors are doing about it and where the gaps remain.
United Natural Foods Inc. shut down its entire information technology (IT) network a year ago after detecting unauthorized access to its systems the day before. The shutdown halted deliveries to 30,000 retail locations across North America, including Whole Foods Market stores.
Shelves went empty. Manual processes replaced automated ones in 10 days. When the damage was tallied, the Providence, Rhode Island-based distributor estimated it would lose between $350 million and $400 million in fiscal 2025 sales.
One month later, Ingram Micro Holding Corp. disclosed that ransomware had been found on its internal systems. The Irvine, California-based technology distributor, which reported $48 billion in net sales in 2024, took its infrastructure offline over the July 4 holiday weekend. Order processing was disrupted globally for approximately one week. The SafePay ransomware group later claimed responsibility and said it had stolen 3.5 terabytes of data. 42,000 individuals were subsequently notified that their personal information had been compromised.
UNFI and Ingram Micro are not isolated cases. They are the most recent entries in a pattern that now spans four major public distributors in less than three years and has produced more than $1 billion in combined revenue losses, stock declines and operational damage.
The Federal Bureau of Investigation’s Internet Crime Complaint Center recorded more than one million cybercrime complaints in 2025, with losses surpassing $20.8 billion for the year. That is a 26% increase from 2024. Business email compromise alone accounted for $3.05 billion of those losses, according to the FBI’s 2025 IC3 Annual Report.
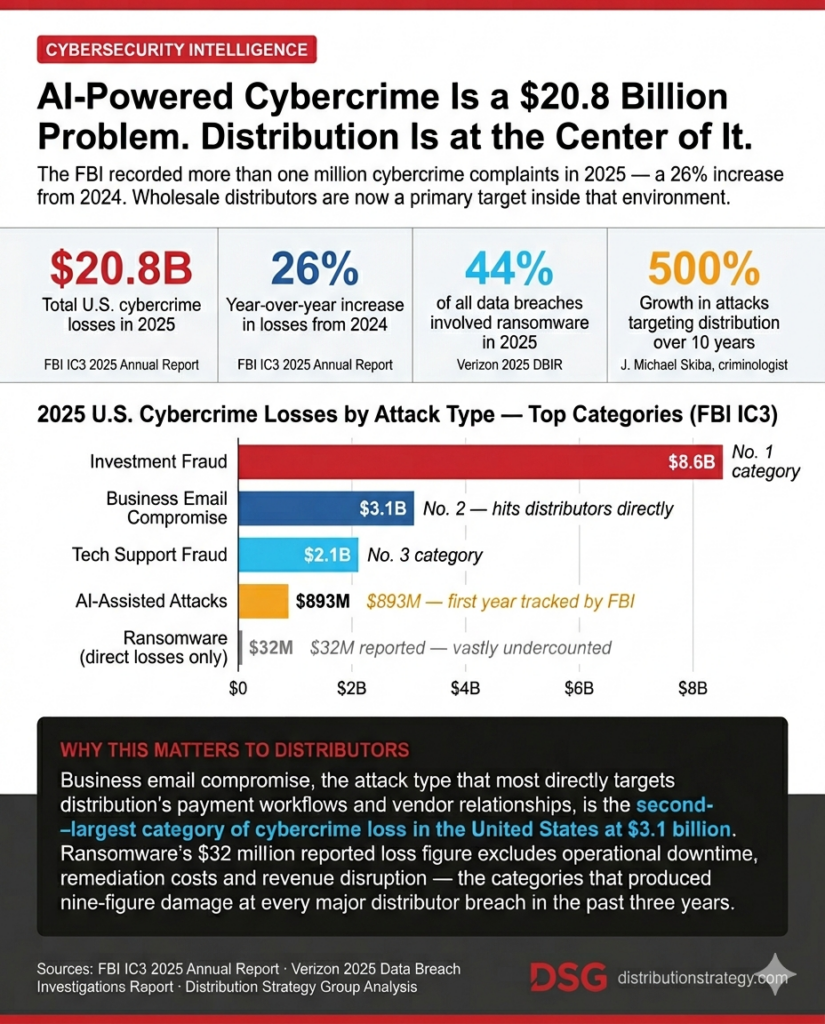
Ransomware appeared in 44% of all reviewed data breaches in 2025, according to Verizon’s annual Data Breach Investigations Report. The number of distinct ransomware extortion groups operating globally reached a record 85 in the third quarter of 2025, according to Check Point Research.
Wholesale distribution is now a primary target inside that environment. And the sector, according to two experts with direct field experience investigating the criminal organizations behind these attacks, is not equipped to handle what is coming at it.
“Distribution is a high-trust, high-volume, high-transaction environment and it operates without the bank protocols that are in place in financial services,” said J. Michael Skiba, a fraud expert who is known as Dr. Fraud and behavioral criminologist who has worked with Interpol and the United Nations on transnational cybercrime cases. “That’s why criminal enterprises have moved so deliberately into this space. I’ve talked to organized criminal groups that have told me that firsthand. They’re dumping millions of dollars in effort into penetrating distribution companies.”
The case for treating cybersecurity as a strategic business priority, not an IT budget line, is written in the earnings reports of the companies that have already been hit.
UNFI’s stock fell 7% when the company announced its breach on June 9, 2025, and dropped more than 10% the following day, a combined decline of approximately 17% in 48 hours. One analyst publicly noted the stock had begun declining before the official announcement, including a 9% drop on June 3 and a 4% drop on June 4, raising questions about whether some market participants had advance awareness.
CEO Sandy Douglas told analysts the company had engaged “all the authorities” and reported “all that we know” to the FBI. No ransomware group publicly claimed responsibility.
Beyond the stock impact, UNFI projected a pre-tax and free cash flow loss of between $65 million and $75 million from the incident. The company incurred $20 million in expenses implementing manual processes and preventing spoilage, plus an additional $5 million on cybersecurity experts, legal assistance, and other direct incident costs.
The Henry Schein Inc. breach in October 2023 remains the most documented case of financial damage from a distribution cyberattack. The Melville, New York-based distributor of medical and dental supplies, a Fortune 500 company with more than $12 billion in annual revenue, discovered a ransomware intrusion on Oct. 14, 2023. The attack was claimed by the BlackCat/ALPHV ransomware group, which said it had encrypted files and exfiltrated 35 terabytes of sensitive data.
What distinguishes the Henry Schein case is what happened after the initial breach. The company had nearly completed its recovery when BlackCat re-encrypted its files a second time on Nov. 22, after negotiations stalled, forcing Henry Schein to begin the recovery process again from the start.
CEO Stanley Bergman told analysts on a November 2023 earnings call that distribution business orders the week of Nov. 6 through 10 were running at 85% to 90% of pre-incident levels. The company cut its full-year 2023 sales forecast from guidance of 1% to 3% growth to a projected decline of 1% to 3%. William Blair analysts said that swing implied a $500 million revenue headwind.
The fourth quarter damage was larger. Henry Schein reported an estimated $350 million to $400 million incident impact on fourth-quarter net sales and a $120 million to $130 million impact on operating income. The company subsequently reduced its 2024 sales growth target from 8% to 10% down to 4% to 6%. Bergman told analysts the pace of recovery “has been slower than anticipated.”
Sysco Corp. disclosed a breach in 2023 as well. Attackers gained access to the global foodservice distributor’s systems on Jan. 14, 2023. Sysco did not discover the intrusion until March 5, two months later. The breach affected 126,243 current and former employees, with names, Social Security numbers and account numbers exposed, according to a filing with the Maine Attorney General. Sysco subsequently faced class action litigation and agreed to a $2.3 million settlement.
All four companies had mature IT departments, dedicated security resources and, in most cases, active cyber insurance coverage when attackers gained access. For the thousands of mid-market and regional distributors operating without those resources, the exposure is measurably higher.
Skiba estimates the volume of cyberattacks against the distribution industry has grown 500% over the past decade. He does not describe that growth as coincidental.
During a United Nations undercover operation in Eastern Europe, law enforcement infiltrated what Skiba described as a criminal trade conference. Approximately 45 individuals from organized crime groups conducted structured sessions analyzing which industries to prioritize for attacks.
“They had steering meetings and committees. They would brainstorm. They had panels,” Skiba said. “They were talking about what industries to focus on. One participant said he’d worked in banking for five years and that was no longer a good play. Distribution came up as a major focus. These things really happen.”
The structural reason is straightforward. Distribution companies process payment volumes and transaction velocity comparable to banks, but they operate without the regulatory oversight, fraud infrastructure, or security investment that financial institutions have built over decades.
“A lot of these distribution companies don’t even have cybersecurity as something separate from IT,” Skiba said. “They think it just sits in IT. That’s not the case anymore. It sits in every single ecosystem, every part of the distribution channel.”
Tim Bertschmann, founder of Bertschmann Group, a technology consultancy with 30 years of experience serving mid-market distributors, puts the industry’s overall cybersecurity posture at a C or below. Skiba’s assessment is the same.
“The employee continues to be the weakest link,” Bertschmann said. “AI advances have allowed the bad guys to hire less expensive employees and use less expensive tools to target a larger victim market. They can attack each part of the distribution chain more frequently and more efficiently.”
The introduction of artificial intelligence (AI) into the criminal toolkit has not simply made attacks faster. It has restructured who can launch them, at what cost and at what scale.
Bertschmann and Skiba identify five AI-enhanced attack vectors now targeting distribution operations.
The first is AI-powered phishing and business email compromise. Attackers use AI to map how a target executive communicates, including cadence, signature style, preferred salutations, and typical subject lines, then generate messages that pass the pattern-recognition filters most employees rely on informally.
Skiba demonstrated the technique during a CEO training session. Using publicly available LinkedIn data, company bios, speaking event recordings and social media posts, he built a detailed profile of a distribution company’s chief executive within 10 minutes, generated an AI voice clone from five seconds of audio and produced a personalized impersonation email from the profile.
“The AI bot scrubbed all the information and understood how he normally talks, how he signs his emails, whether he uses dashes, whether he says ‘hey’ and it was very, very personable,” Skiba said. “When I showed the CEO what the campaign against him would actually look like, that was the moment. He understood that his CFO could have been tricked by that email.”
The second vector is automated reconnaissance. Before any phishing campaign or wire fraud attempt is launched, AI tools systematically map an organization’s structure by pulling from LinkedIn profiles, company websites, breach databases, vendor portals, and public-facing Microsoft 365 configurations.
“The attack often starts weeks before the fraud event,” Bertschmann said. “Attackers map executives, vendors, payment workflows, exposed systems and employee roles before they ever make contact. Instead of random phishing, they target the right person at the right time with highly personalized attacks.”
The third vector is deepfake voice impersonation. Skiba said he can produce a voice clone from five seconds of audio in under a minute using commercially available AI tools. That capability is being used against distribution purchasing departments, where a caller impersonating an executive or vendor can verbally authorize a wire transfer, approve a shipment change or modify payment details without triggering any formal approval workflow.
The fourth vector is ransomware automation. AI assists in automating ransomware deployment after initial access is established, including identifying and disabling backup systems before the encryption payload executes. The compressed timeline that results leaves defenders with less time to detect and contain the intrusion.
“Tested, offline or immutable backups are now a basic requirement,” Bertschmann said. “Not having them is not an oversight. It is an open door.”
The fifth vector is invoice and accounts payable fraud. In one case Skiba described in detail, attackers gained access to a distributor’s accounts payable environment and spent two weeks silently observing, mapping who approved wire transfers and studying vendor communication patterns before generating fraudulent invoices with AI. The accounts payable manager processed six or seven fraudulent payments totaling approximately $300,000 before the fraud was detected.
“What normally would have taken 10 people on the criminal side five years ago,” Skiba said, “was one person behind the curtain clicking buttons and letting the AI do the work.”
The barrier to entry for these attacks has effectively disappeared. Skiba identified a dark web subscription service, priced at approximately $400 per year, which provided an AI-powered fraud toolkit to more than 2,200 subscribers. The software automated target research and guided users through each step of the attack.
“With $500, you can get an AI toolkit that will tell you to look at a person’s LinkedIn, check their WhatsApp, map their payment workflows,” Skiba said. “The barrier to entry is almost non-existent.”
Distribution companies frequently run enterprise resource planning (ERP) systems and telecommunications infrastructure that have not been updated in years. That legacy environment actively creates entry points that AI-powered reconnaissance tools catalog and exploit.
Bertschmann said the gaps he consistently encounters after a cyber incident include open firewall ports, outdated ERP systems, legacy phone systems requiring frequent patching, unfounded assumptions that cloud providers handle all security on the client’s behalf and payment systems with no documented procedural controls.
“There are still some customers running voicemail servers on Windows 95,” Bertschmann said. “Any outdated equipment connected to the network is a cyber risk. Those systems can be a vector for internal infection and spreading.”
Legacy Voice over Internet Protocol (VoIP) systems present a specific and underestimated vulnerability. Equipment from vendors that no longer issue security patches can serve as a network entry point that bypasses more hardened modern infrastructure.
Third-party integrations extend the exposure further. Electronic data interchange (EDI) connections to suppliers, ERP links to logistics platforms and vendor portal access each represent trusted pathways into a distributor’s operational environment.
“Many distributors secure their internal network but overlook vendor and supplier access, which often has direct visibility into orders, payments and customer data,” Bertschmann said. “A compromised vendor connection can lead to fake purchase orders, payment diversion, shipment rerouting or invoice manipulation that looks completely legitimate. In distribution, companies assume known vendors are safe. Attackers exploit that assumption systematically.”
multi-factor authentication (MFA) adoption is partial at best. Bertschmann said most distributors have deployed MFA for email and stopped there, leaving virtual private network (VPN) access, ERP systems, and administrative accounts unprotected. Shared accounts in warehouses and operations centers compound the problem by eliminating transaction-level accountability.
“The biggest failure is not technology. It is exception culture,” Bertschmann said. “Many still see MFA as an IT inconvenience instead of a fraud prevention control tied directly to money movement.”
The organizations behind these attacks are not individuals probing networks opportunistically. Skiba’s field work with Interpol and the United Nations brought him into direct contact with the entities now targeting distribution on scale.
“These are highly, highly organized criminal enterprises,” Skiba said. “I’ve seen cases where organizations had pivoted off traditional methods, drug trafficking, human trafficking, and moved to cybercrime because it was less risky and significantly more rewarding.”
During his United Nations rotation in Southeast Asia, Skiba documented a facility across the Myanmar border with more than 50 servers and a staff recruited specifically for cybercrime operations. These were structured businesses with capital allocation, research functions and performance management, not opportunistic actors.
The targeting methodology is systematic. Criminal organizations identify candidate companies in a target vertical, run low-level probes against each to test whether detection protocols exist and escalate against the companies that do not respond.
“They shoot one off the bow,” Skiba said. “If they get away with it, they do a little more, a little more, a little more. They’re looking for the weakest link in the pack. The distribution industry looks like that weakest link right now.”
Before any direct contact is made, criminal teams spend weeks researching individual executives, mapping payment approval chains and learning communication patterns from public records, social media and speaking events.
“By the time they pounce, whatever that is, a text, an email, a phone call, it is so authentic that the CEO is tricked nine times out of 10,” Skiba said. “They play a long game. And the backdoor is open. Once it’s open, it’s like Pac-Man. Game over.”
The distribution industry has not yet adapted to the current generation of AI-enabled attacks. A second generation is already in development.
Agentic AI, meaning autonomous systems capable of executing multi-step tasks without human supervision, is beginning to appear in legitimate business-to-business (B2B) commerce workflows for procurement, payment processing, and inventory replenishment. The criminal application of the same technology threatens to automate fraud simultaneously across multiple targets at a speed no human-supervised response can match.
“Right now, all you need is one person behind the curtain directing the AI,” Skiba said. “An autonomous agent is going to be able to run five of those fraud scenarios simultaneously and make the right decisions in real time without going back to anyone for approval. That’s what worries me. We’re not even at a B-plus level dealing with the first wave. If the second wave comes, we’re going to be in serious trouble across the board.”
Synthetic identity fraud is an early marker of what that next wave looks like. AI-generated vendor identities, complete with documentation, account histories, digital communication patterns and verifiable-looking credentials, are being used to infiltrate vendor onboarding at distribution companies that have not formalized verification protocols. Once a synthetic vendor is established in an accounts payable workflow, the fraudulent payment infrastructure is in place and self-sustaining.
The financial trajectories at Henry Schein, Sysco, UNFI and Ingram Micro illustrate the stakes. Henry Schein absorbed an estimated $500 million revenue headwind and a multi-quarter earnings restatement. Sysco faced two years of class action litigation. UNFI watched its stock drop 17% in 48 hours while Whole Foods shelves went empty in real time. Ingram Micro lost a week of global order processing capacity at the height of a summer business cycle.
Those are the cases that made it into SEC filings and earnings calls. For every publicly disclosed breach at a major distributor, an unknown number of incidents at regional and mid-market companies are absorbed quietly and never reported.
“I would simply tell that CEO that they are a target,” Bertschmann said. “It is not a matter of if. It is a matter of when. And raising your hand and asking for help with your cyber program is not a sign of weakness. It is your duty.”
AI-powered cybercrime has moved from a technology risk to a business continuity risk. The four major distributor breaches documented here produced more than $1 billion in combined financial damage across companies with enterprise-grade security resources. For mid-market and regional distributors operating without those resources, the exposure is larger, not smaller.
*Part Two: What Distributors Are Doing, Investment Patterns, Control Adoption and What Still Needs to Change, published next week. *
Share this article: