Editor’s Note: This is Part Two of a two-part series examining AI-powered cybercrime targeting wholesale distributors. Part One documented the scale of the threat, including four major distributor breaches that produced more than $1 billion in combined damage, drawing on field research and interviews with fraud expert J. Michael Skiba and technology consultant Tim Bertschmann. This installment examines what distributors are doing about it and where major security gaps remain.
The call came from what sounded exactly like the company’s chief financial officer. The voice, the cadence, even the familiar shorthand the two colleagues used matched precisely. The CFO needed a wire transfer processed immediately. A vendor deal was closing. The window was narrow.
The finance manager processed the transfer. The CFO had never made the call. The voice was a synthetic clone generated from audio scraped from a company webinar posted publicly months earlier. By the time the fraud was detected, the money was gone.
That is not a hypothetical. It is one of the growing numbers of artificial intelligence-enabled fraud events hitting wholesale distributors, most of them never reported publicly and most absorbed as operational losses by companies that did not want customers, vendors, or competitors to know how exposed they were.
AI has given criminal organizations the ability to impersonate executives using their own voices, construct vendor identities from scratch, personalize phishing emails with details no generic scam would know and deploy ransomware with a precision that disables backup systems first. The attacks are faster. The losses are larger. And the distribution industry, built on trust, long relationships and high-volume payment flows, sits at the center of the target.
The Infrastructure Gap
Tim Bertschmann, founder and president of the Bertschmann Group, has spent 30 years advising organizations on information technology infrastructure, telecommunications, and cybersecurity. He said the distribution sector’s technology environment is structurally mismatched with the current threat.
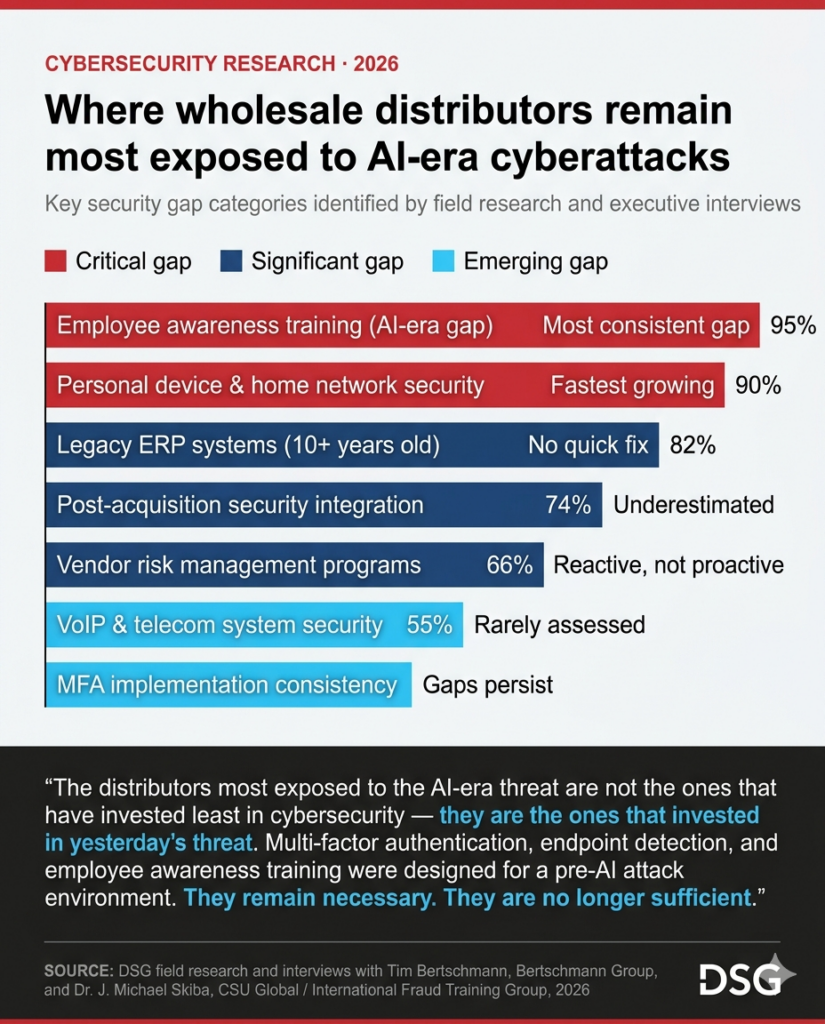
Many mid-market distributors run enterprise resource planning, or ERP, platforms that are years, sometimes decades, behind current security standards. Authentication requirements are weak. Audit logging is limited. Vendor integrations are extensive and poorly monitored. AI-powered reconnaissance tools can map an organization’s entire technology footprint from public information before a single intrusion attempt is made, Bertschmann said.
“The attacker knows more about a mid-market distributor’s infrastructure than most of that company’s own employees do. Job postings tell them the ERP platform,” he said. “LinkedIn tells them the IT staff size. Press releases tell them about vendor relationships. AI assembles all of it in minutes.”
Voice over Internet Protocol, or VoIP, and telecommunications systems are among the most underprotected entry points in the distribution environment, Bertschmann said. As distributors have migrated to hosted phone systems and unified communications platforms, they have created pathways attackers can exploit for call interception, credential harvesting and deepfake audio fraud. The business phone system is rarely part of a distributor’s cybersecurity assessment, he said. It should be.
AI voice-cloning tools draw on audio from voicemail systems, conference call recordings, and public presentations. A CFO’s outgoing voicemail greeting can be enough raw material to generate a convincing impersonation. Fraud does not require a sophisticated criminal operation. It requires an AI tool and a phone number.
The insurance market has become the most effective forcing function for mid-market distributor cybersecurity investment, Bertschmann said. Carriers now require multi-factor authentication, endpoint detection, and documented incident response plans as conditions of coverage. Companies that cannot demonstrate those controls are finding policies unavailable or prohibitively priced. Insurance requirements are creating hard deadlines for security upgrades that years of internal advocacy could not.
Post-acquisition security integration is the risk he finds most consistently underestimated in distribution mergers and acquisitions. An acquirer that connects a newly purchased company’s systems to its own network without a security assessment inherits every vulnerability the acquired company carried. In a sector where acquisition activity has been significant for a decade and technology due diligence has historically been an afterthought, that inherited exposure is often substantial, Bertschmann said.
J. Michael Skiba chairs the criminal justice department at Colorado State University Global and serves as president and co-founder of the International Fraud Training Group. Known professionally as Dr. Fraud, he has delivered more than 400 keynote addresses on fraud and cybercrime and has trained investigators and executives for the United Nations, INTERPOL, the Federal Bureau of Investigation and the Bureau of Alcohol, Tobacco, Firearms and Explosives. He has more than 20 years of direct fraud investigation experience.
Cybercriminals are not technologists, Skiba said. They are entrepreneurs operating in an unregulated market with low fixed costs, asymmetric risk, and high return potential. AI has reduced their variable costs to near zero. What previously required a team of skilled social engineers now runs as an automated workflow that any criminal organization with modest resources can deploy at scale against distribution targets.
“AI did not change the psychology of fraud. It industrialized it,” Skiba said. “The distributor executive who thinks his company is too small to be a target does not understand that AI has eliminated the economics that made small targets unattractive.”
Most distributor security programs are missing what Skiba calls the hacker’s perspective: the specific steps an attacker takes from initial reconnaissance through the moment of financial loss or system compromise. Compliance training explains what to do. The hacker’s perspective explains what is being done to you. That sequence, made concrete and specific, changes executive behavior in a way that a policy seminar does not, he said.
In a typical session with a distribution company leadership team, Skiba demonstrates how an AI tool builds a target profile from publicly available information: the chief executive officer’s LinkedIn activity, the CFO’s conference presentation audio, the accounts payable manager’s email address pulled from a vendor directory. Those inputs generate a personalized phishing email, a convincing vendor impersonation and, in the most direct demonstration, a deepfake audio clip simulating the CEO instructing a wire transfer. The session takes less than an hour. The behavioral change it produces, Skiba said, outlasts annual compliance training.
The psychological mechanisms AI exploits are not new. Urgency, authority, and familiarity are the same tools social engineers have always used to override human judgment. What AI has changed is the precision of deployment. A phishing email that arrives the morning after an executive attended an industry conference, references a specific vendor relationship and mimics the CEO’s writing style does not trigger the same skepticism as a generic password-reset request. Personalization defeats the instincts people have developed to detect fraud.
Business email compromise is the financial crime that most directly threatens distributor cash flow and most consistently succeeds against mid-market companies that believe their controls are adequate, Skiba said. In the fraudulent payment redirection scenario, a vendor’s email is compromised or impersonated and banking credentials are updated in the distributor’s accounts payable system. The fraud is patient and precise. AI has made both cheaper.
Protecting the Person, Not Just the Company
Bertschmann and Skiba both point to a dimension of the threat that most corporate cybersecurity frameworks do not address: the personal attack surface of the executive.
A distribution company’s security policy governs corporate devices, corporate accounts, and corporate networks. It does not govern the CEO’s home Wi-Fi network, the CFO’s personal email, the chief operating officer’s family members’ devices, or the personal banking relationships of a high-net-worth executive whose equity represents years of accumulated financial exposure. The personal environment is often both less protected and more financially valuable to an attacker than the corporate one.
Skiba’s Executive Cyber Body Guard program is designed to harden the personal attack surface alongside the corporate one. It combines an ongoing education program for executives and their families with active monitoring of personal credential exposure, digital footprint, and account compromise indicators.
The family dimension is the element that most consistently surprises executives when they engage with the program, Skiba said. A teenager’s social media account can expose a family’s home address. A spouse’s compromised email account can provide an attacker with access to shared financial accounts. An executive’s personal cyber risk does not exist in isolation from the household around it.
Showing an executive a real-time demonstration of how their personal data surfaces on a dark web forum, or how a 30-second audio sample from a public speech generates a convincing voice clone, converts abstract risk into concrete urgency, Skiba said. The goal is not to paralyze. It is to produce informed, permanent behavioral change that extends from the office to the home.
What Distributors Are Doing
The distributor response to cybersecurity investment tracks closely with company size and ownership structure. Large public distributors with dedicated information technology organizations and regulatory disclosure obligations have built more structured programs. Mid-market and family-owned companies, which represent much of the industry by count, have moved more slowly, often investing reactively after an incident rather than proactively before one.
AI has compressed the timeline for reactive response. The attacks are faster, more personalized, and more difficult to detect at the human review level where most mid-market distributor fraud controls are concentrated.
Multi-factor authentication on email and ERP systems is the most widely deployed control in the distribution sector, driven by insurance carrier requirements as much as by internal security investment. Implementation remains inconsistent. Remote sales forces, field-based employees, and executives who resist the friction of additional authentication steps create gaps that attackers have learned to target.
Endpoint detection and response platforms have moved from large-distributor technology into the mid-market, in part because managed security service providers have made them accessible to companies without dedicated internal security staff. The more sophisticated platforms incorporate AI-assisted anomaly detection, flagging unusual network behavior, abnormal file access patterns and credential use that deviate from established baselines.
Tabletop incident response exercises have become a requirement from both insurance carriers and key customers. A distributor that cannot demonstrate a documented, tested incident response capability is finding that liability exposure extends beyond the insurance market into customer contract terms. Large manufacturers and retailers that depend on distributor partners for supply chain continuity are beginning to treat cybersecurity posture as a vendor qualification criterion.
Vendor risk management programs have expanded at distributors that experienced supply chain compromise attempts or received guidance from insurance carriers about third-party exposure. A distributor’s security posture is only as strong as the weakest connection in its vendor network. An electronic data interchange, or EDI, integration with a small logistics partner, a remote access credential issued to a legacy software vendor or a cloud-based ERP connection that was never properly permissioned is an entry point that AI-powered attackers can identify and exploit faster than most distributor information technology teams can audit.
Where Distributors Remain Exposed
Employee training is the most consistent gap between what distributors believe they are doing and what security professionals find when they assess those programs. Annual awareness training treats cybersecurity as a compliance event. AI-era attacks require behavioral change that is current, specific, and continuously reinforced. An employee who completed phishing awareness training 11 months ago has not been prepared for an AI-generated phishing email that references a colleague by name, cites a real project, and arrives from a legitimate vendor domain.
Personal device and home network security for executives and remote employees is the fastest-growing attack surface in the distribution sector and the least consistently addressed. The shift to remote and hybrid work created permanent connectivity pathways between corporate systems and home environments that most distributor security policies have not fully closed. An executive who accesses the company ERP from a home network running consumer-grade hardware has created an attack surface that no corporate firewall can protect.
Legacy ERP systems are a structural vulnerability without a quick fix. Distributors running platforms that are 10 or more years old are operating on systems that were not designed to defend against current credential attack patterns, do not produce the audit log detail that incident response requires and may not support the authentication controls that modern security practice demands. Replacing those systems is a multi-year commitment. The exposure they represent is active in the interim.
Post-acquisition integration failures are an underappreciated source of cyber exposure in a sector where merger and acquisition activity has been significant for the better part of the decade. Companies being acquired are often smaller, less technology-mature organizations whose security posture was never assessed during due diligence. When their systems connect to an acquirer’s network, the inherited vulnerabilities travel with them.
A Distributor’s Account
A distributor in the Midwest experienced a ransomware attack that took its enterprise resource planning system offline for more than three weeks. Order processing reverted to phone calls and manual entry. Customer service response times deteriorated. Several long-standing accounts placed emergency orders with competitors. The company’s cyber insurance covered a portion of the remediation cost. It did not cover the customer relationships that required months to rebuild.
The distributor’s leadership team, which had previously treated cybersecurity as an information technology department responsibility, convened within 48 hours of the attack. The decisions made in those two days, whether to pay the ransom, which customers to notify first, how to communicate the disruption to a workforce operating without digital systems, were consequential and irreversible.
The incident changed the company’s approach to cybersecurity in ways that prior investment proposals had not. The chief executive authorized security spending that had been deferred for three consecutive budget cycles. An executive education program was engaged. The company built and evaluated an incident response plan within 90 days of the attack. No such plan had existed before it.
The total cost of the ransomware event, including remediation, lost revenue and operational disruption, exceeded the cumulative security investment the company had deferred over the prior three years. The operational and relationship costs were not insurable.
That sequence, deferral followed by incident followed by forced investment, is the most common pattern in distributor cybersecurity. It is also the most expensive.
What the Next 24 Months Bring
The AI threat facing wholesale distributors is not a static target. The tools available to cybercriminals are advancing on a timeline that outpaces most distributor security investment cycles. Three developments are reshaping the threat trajectory for the distribution sector.
The current generation of AI-powered cybercrime still involves human decision-making at key points: selecting targets, initiating contact, authorizing transfers. The next generation will not. Autonomous attack agents, AI systems that identify targets, conduct reconnaissance, execute social engineering, and trigger financial transactions without human intervention, are actively developing by criminal organizations with significant resources. For distribution companies whose accounts payable and receivable workflows involve high-volume payment activity with established counterparties, that development represents a qualitatively different threat than anything the sector has previously faced.
Business email compromise has historically required attackers to compromise a real email account or create a convincing spoof of one. AI-generated synthetic identities eliminate that requirement. Attackers can now create fully backstopped vendor profiles, complete with website, email domain, phone number, professional history, and fabricated references, which pass the verification checks most distributor procurement and accounts payable workflows apply to new vendors. A synthetic vendor that enters a supplier database through a plausible onboarding process, builds a payment history over several months and then redirects a large transaction to a fraudulent account is a fundamentally different operational risk than a phishing email a trained employee can identify and delete.
The next generation of AI-powered phishing will be adaptive, adjusting content, tone and timing based on a recipient’s real-time responses and escalating through multiple communication channels simultaneously. A campaign that begins with an email, follows up with a phone call using a cloned voice and closes with a text message citing details from the prior exchanges will not match any threat pattern employees have been trained to recognize. The attack adapts faster than the training program updates.
The cyber threat facing wholesale distributors is not exceptional in its novelty. Criminal organizations have targeted financial institutions, retailers, and industrial companies for decades. What is exceptional is the combination of timing and technology. Artificial intelligence has arrived at a moment when the distribution sector’s technology infrastructure is in transition, its workforce is dispersed and its operational reliance on digital systems is deeper than at any prior point in the industry’s history.
The Competitive Stakes
The distributors most exposed to the AI-era threat are not the ones that have invested least in cybersecurity. They are the ones that invested in yesterday’s threat. Multi-factor authentication, endpoint detection, and employee awareness training were designed for a pre-AI attack environment. They remain necessary. They are no longer sufficient.
The distributors building AI-era cyber programs are doing so because their leadership teams have internalized a different threat calculus. The question is not whether an attack will occur. It is whether the company will be operationally and financially capable of surviving it when it does.
Bertschmann puts the investment decision in terms that resonate with executives in a margin-compressed, working-capital-sensitive business. The cost of a structured cyber defense program is a fraction of the average ransomware recovery cost in the industrial sector. The financial argument for proactive investment is not complicated. The companies not making it are not lacking the arithmetic. They are lacking urgency.
The executives who have sat through a real-time demonstration of how AI assembles their personal and professional attack surface do not leave asking whether the threat is real, Skiba said. They leave asking how quickly they can act.
The AI tools being used against wholesale distributors do not distinguish between a $50 million regional company and a $5 billion national one. The attack surface is the system, the payment workflow, and the person on the other side of the screen. All three are present in every distribution company in the country.
Share this article: